Quick Summary
As BAS shift from isolated networks to hybrid and cloud-connected architectures, securing connectivity becomes foundational—not optional. Device-level Zero Trust, segmentation, encrypted communications, strong remote access control, and unified monitoring are essential. Buildings that embrace secure connectivity can safely adopt cloud innovation while maintaining resilience, safety, and trust.
Introduction
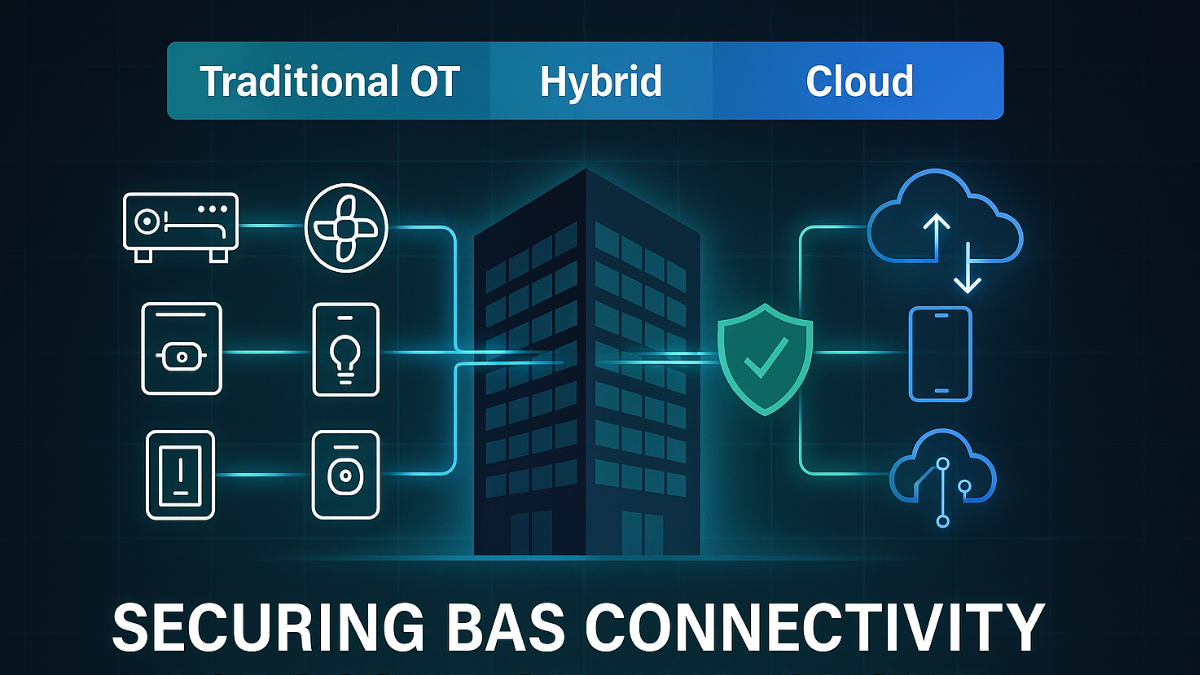
Building Automation Systems (BAS) are undergoing a transformation. What started as isolated, on-premises control networks has evolved into hybrid architectures that blend local supervisory control with remote management, vendor portals, analytics platforms, and cloud-based dashboards. Many buildings are already moving toward fully cloud-connected BAS ecosystems, enabling advanced optimization, remote serviceability, digital twins, and more integrated operational workflows.
But with increased connectivity comes increased cyber exposure. Facilities that once relied on physical separation or simple VLANs now face threats that span local OT networks, corporate IT environments, and external cloud systems. The challenge is clear: secure connectivity must be engineered into the BAS lifecycle, not added as an afterthought.
This article explains how BAS connectivity models are shifting, the risks associated with that shift, and how building owners and operators can secure BAS across traditional, hybrid, and cloud environments.
The Three Phases of BAS Connectivity
Smart buildings rarely move from offline to cloud overnight. Instead, they follow an adoption curve:
- Traditional BAS (Local, Isolated OT Networks)
Historically, BAS networks were:
- Physically isolated (“air-gapped”)
- Controlled only from on-premises workstations
- Operated on legacy, interoperable but insecure protocols (e.g., BACnet, Modbus, KNX)
- Considered outside the scope of cybersecurity
While operationally simple, these networks now face threats from internal users, USB-borne malware, vendor laptops, and accidental bridging to corporate networks.
- Hybrid BAS (Local + Cloud + Remote Access)
Most modern buildings reside here. Characteristics include:
- Local control but cloud-enabled dashboards
- Vendor remote access for maintenance
- Integration with corporate IT for reporting and analytics
- Partial use of APIs and connected systems
Hybrid BAS dramatically expands the attack surface. Misconfigured remote access, exposed endpoints, flat internal networks, and unencrypted OT protocols create opportunities for ransomware and credential-based attacks.
- Fully Cloud-Connected BAS
Emerging systems shift supervisory control, analytics, energy optimization, and scheduling entirely to cloud platforms. This unlocks innovation but demands stronger cybersecurity practices:
- Credential security and MFA
- Secure APIs and OAuth workflows
- Cloud-to-edge Zero Trust architectures
- Continuous monitoring and anomaly detection
Without these foundations, cloud-centric BAS become high-value targets for cybercriminals.
Why Secure Connectivity Matters More Than Ever
As BAS connectivity grows, so do threats:
Increased attack pathways
A compromise on an IT asset—such as a contractor laptop or a cloud credential—may allow attackers to pivot into BAS networks.
Legacy devices cannot protect themselves
Many BAS devices lack encryption, authentication, or secure boot. They rely on network controls and overlays to stay protected.
Regulatory pressure is rising
Frameworks such as NIST CSF 2.0, DoD Zero Trust, and the EU NIS2 Directive require continuous verification, segmentation, and strong authentication for operational systems.
Operational impact is higher than data-only breaches
BAS cyber incidents can:
- Disrupt HVAC in hospitals
- Lock tenants out of buildings
- Impact safety and comfort
- Increase energy costs
- Damage trust and reputation
Building operators cannot rely solely on traditional IT controls. BAS requires OT-aligned protection that can adapt to mixed environments.
Strategies for Securing BAS Across Traditional, Hybrid, and Cloud Networks
- Adopt Zero Trust at the Device Level
Zero Trust replaces implicit trust with continuous verification. Every device must prove its identity before it communicates.
- Enforce cryptographic device identity
- Authenticate every command
- Encrypt all communications
This is essential for insecure protocols like BACnet, Modbus, and KNX.
- Segment OT From IT—and Then Segment Further
Flat networks are attackers’ best friends.
- Separate HVAC, access control, lighting, elevators, and metering
- Use micro-segmentation for critical controllers
- Enforce firewall and VLAN boundaries
Segmentation limits blast radius and prevents lateral movement.
- Secure Remote Access & Vendor Management
Most BAS breaches begin with mismanaged remote entry.
Implement:
- MFA for all remote connections
- Role-based and least-privilege policies
- Time-bound access
- Secure jump hosts or Zero Trust brokers
- Logging and auditing for third-party activity
- Encrypt and Authenticate All BAS Traffic
Even in traditional systems, traffic should never be plaintext.
Use:
- Encrypted overlays for BACnet/Modbus
- TLS or certificate-based tunnels
- PQC-ready (post-quantum cryptography) algorithms where possible
- Align OT Network Monitoring With IT Monitoring
Hybrid and cloud BAS require unified visibility.
- Baseline normal behavior
- Alert on anomalous commands
- Correlate OT telemetry with IT security platforms
- Use Crypto-Agile, Future-Proof Solutions
Because BAS devices last 10–20 years, choose solutions that can:
- Update cryptographic algorithms
- Support PQC in the future
- Integrate with Zero Trust architectures
Crypto agility ensures long-term security as standards evolve.
Key Takeaways
- BAS connectivity is evolving from traditional to hybrid to full cloud, increasing cyber exposure.
- Zero Trust and device-level authentication are essential for modern BAS security.
- Legacy protocols require encrypted overlays to ensure secure communication.
- Vendor and remote access must be tightly controlled with MFA and least privilege.
- Unified monitoring across IT and OT ecosystems prevents blind spots.
- Crypto agility prepares buildings for long-term changes, including post-quantum security.


