IoT and OT Cybersecurity Products and OEM Toolkits

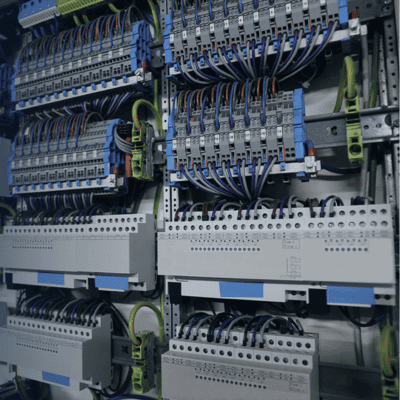
OT Cybersecurity (Retrofit)
Security solution for protecting new and existing automation systems and other critical building Operational Technology (OT)
- NIST-compliant Zero Trust framework
- Device-level protection
- Authentication
- Data Encryption
- Post-Quantum Ready
- Retrofit existing building networks
Device Ownership Management and Enrollment (OEM / Embedded)
Embedded cybersecurity software for protecting automation systems, Operational Technology (OT), and IoT devices
- Transfer ownership in the field and securely connect to a device without a network or cloud connection
- Creates a unique lifetime pedigree for each device in a blockchain
- Requires only 8K of ROM to implement, ideal for the smallest IoT devices
- Zero-touch, enables the secure installation of devices, even for those with no user interface

