Veridify is a proud Intel Titanium partner. We offer fast, quantum-resistant identification, authentication, and data protection solutions on Cyclone® V SoC and MAX® 10 FPGAs. Our solutions can be used for secure communication with other Intel FPGAs, CPUs, devices running on 8- to 32-bit processors, or microcontroller endpoints. These solutions are ideal for applications targeting industrial IoT, automotive, defense, consumer and medical markets.
A FREE security toolkit is available now on Intel’s DE10-Nano development kit (Cyclone® V SoC FPGA), an ideal platform for developers who require design flexibility, performance, and expanded I/O options when creating innovative applications for the IoT. To support fast and easy implementation, Veridify provides a complete and free SDK and technical tutorial on authenticating remote devices with a Cyclone® V System-on-Chip (SoC) FPGA, located on the Intel Developer Zone website.
Veridify Security Benefits and FPGA IP Products
Intel FPGA SoC devices are well suited for a wide variety of functions, including acting as an IoT gateway that can authenticate and control hundreds of remote endpoints. The low-resource endpoints that these gateways communicate with and control often run on 8-, 16-, or 32-bit processors. Legacy security methods such as ECC and RSA are computationally too intensive to run on such low-resource devices, thereby limiting the options for strong security that can be implemented (as the same security methods must be run on both on an IoT gateway and the remote endpoint it with which it communicates). Veridify's methods can be used both on the FPGA device as well as the low-resource endpoints, enabling strong security in these heterogeneous environments.
For example, our Bump in the Wire solution combines Veridify’s quantum-resistant security methods with Intel’s Max 10 FPGA to create a security gateway that can be implemented on already- deployed industrial endpoints on the Internet of Things that were designed before the need for security was realized.
Veridify’s security toolkit includes Ironwood™ Key Agreement Protocol (Ironwood KAP) and Walnut Digital Signature Algorithm (WalnutDSA™), which are designed to run on the smallest processors. Based on Group Theoretic Cryptography methods, the computational efficiency of Veridify’s security protocols and algorithms translate into significant performance advantages over legacy security methods. Of special interest to designers of devices with long service lives, Veridify methods are quantum-resistant to all known attacks.
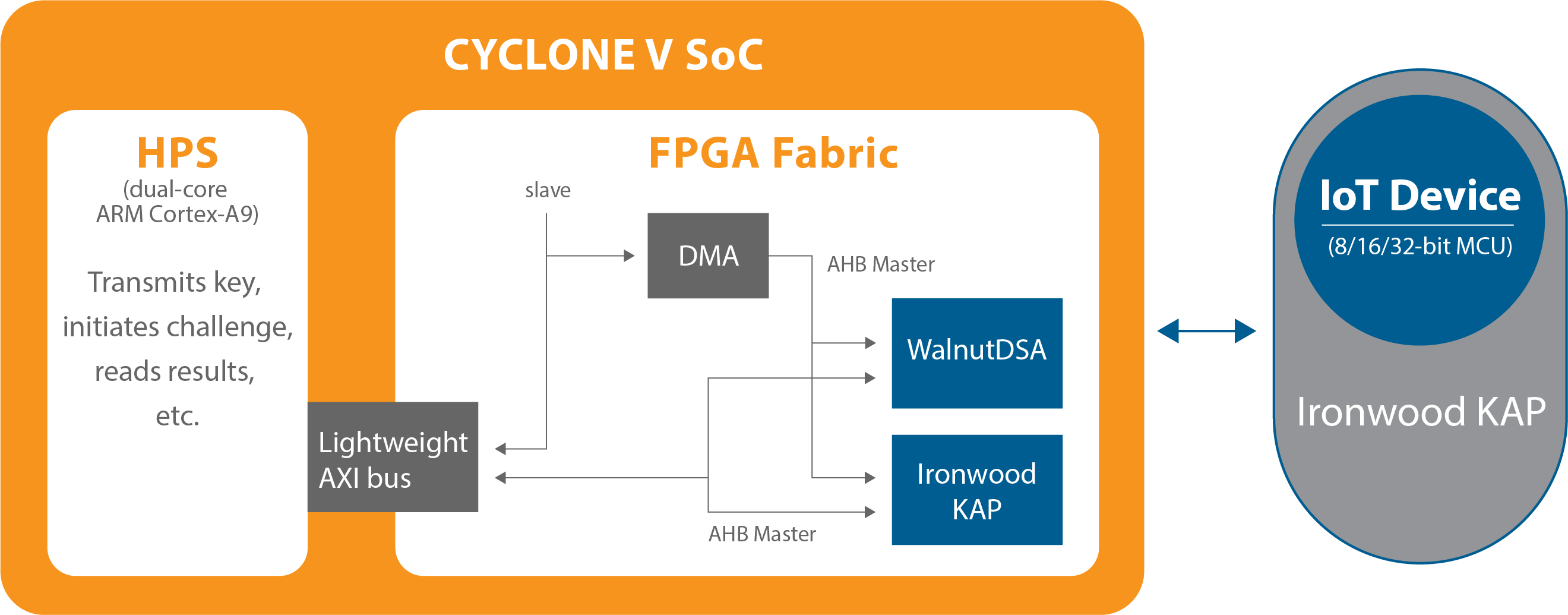
Veridify’s WalnutDSA and Ironwood KAP are implemented as soft IP cores in the programmable logic side of the Cyclone® V SoC with help from the Hard Processor System
Intel FPGA Reference Designs
NovTech Cameleon96 Community Board, available from NovTech or Arrow
This board is fully compliant to the Linaro 96Boards open platform specification and features a Intel Cyclone® V SoC FPGA. It includes Veridify’s quantum-resistant key agreement protocol and digital signature algorithm reference design. Learn more here.
Need Help Implementing Security on Your Devices? Contact us Today!
Our security experts are ready to support you. We offer design services and free consultations.
Retrofit IoT Devices with a Strong Security Solution.
Free Toolkits
Quickly and easily embed our fast, small-footprint, ultra-low-power cryptographic solutions in your IoT devices. Our hardware and software development tools are easily integrated into new or existing platforms. Our SDKs and hardware kits are ideal for Intel FPGAs, as well as the devices they may be connected to whether ASICs, microcontrollers, and other low-resource platforms deployed in the IoT.
Request your free Software Development Kit today.
Educational Resources
Learn more about our partnership with Intel and access valuable training resources to learn how to implement SecureRF security methods here:
Veridify Intel Design Solutions Network (DSN) Partner Profile.
Intel Developer Zone Tutorial – Adapting to Security Threats with FPGAs.
